Key Takeaways
- Appoint a DPO to own privacy accountability.
- Build a living data map across systems and flows.
- Prioritize least‑privilege access and data minimization.
- Run DPIAs for high‑risk uses (e.g., AI, biometrics).
- Document policies, training, and audits to prove compliance.
CNIL privacy compliance is not just a French regulatory requirement—it offers practical lessons for any organization handling personal data. With GDPR compliance steps forming the foundation, CNIL adds its own data protection guidelines that emphasize transparency, accountability, and user rights. Companies that align with French data protection regulations strengthen their overall privacy governance, reduce risk, and build trust with stakeholders. In today’s environment, where data breaches and enforcement actions are increasingly common, building programs around CNIL compliance requirements provides a competitive edge.
Why CNIL Privacy Compliance Matters
The Commission Nationale de l’Informatique et des Libertés (CNIL) serves as France’s data protection authority, enforcing privacy law compliance in France. For businesses, CNIL compliance requirements extend beyond theory. They include concrete expectations like lawful processing, data minimization, and clarity in user consent. Non-compliance often leads to fines and reputational damage, as seen in French CNIL enforcement actions. Companies that proactively implement measures can transform compliance from a burden into a driver of customer trust and operational excellence.
GDPR Compliance Steps with French Regulations
CNIL operates within the broader GDPR framework but tailors enforcement to local contexts. Practical GDPR compliance steps for France include:
- Maintaining records of processing activities (ROPA).
- Ensuring explicit consent aligned with CNIL consent requirements.
- Implementing strong data breach notification CNIL processes.
- Conducting a CNIL privacy audit process at regular intervals.
- Embedding data minimization principles into all data flows.
- Regularly updating privacy notices to reflect CNIL data protection guidelines.
By adopting these steps, companies meet both EU and national privacy law standards while demonstrating accountability to regulators and customers.
Using a CNIL Privacy Compliance Checklist
A privacy compliance checklist CNIL ensures organizations do not overlook critical elements. Effective checklists often include:
- Identifying lawful basis for processing and documenting justification.
- Appointing a Data Protection Officer (DPO) with clear responsibilities.
- Mapping data flows across systems and third-party vendors.
- Conducting CNIL data protection impact assessments before launching projects.
- Establishing a CNIL privacy audit process for continuous improvement.
- Training staff on CNIL privacy compliance rules and their role in implementation.
This systematic approach helps maintain accountability while aligning with French data protection regulations.
High-Risk Processing and DPIAs
CNIL emphasizes the importance of a data protection impact assessment when handling high-risk processing activities like biometrics, AI, or geolocation. Performing a CNIL data protection impact assessment ensures risks are mitigated before deployment. Companies should also document their risk-mitigation measures and establish regular review points. This proactive approach demonstrates commitment to privacy compliance best practices in France and prepares businesses for potential inspections.
Enforcement and Lessons from CNIL
French CNIL enforcement actions highlight that organizations must move beyond policies to active implementation. Key lessons include:
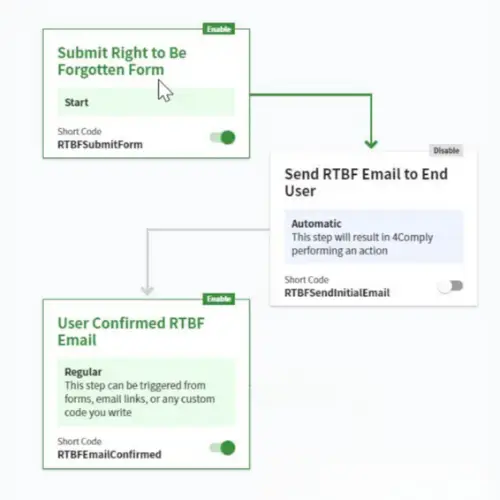
- Prioritize user rights and transparency in every interaction.
- Provide clear consent flows and options for withdrawal.
- Prepare for inspections and audits with up-to-date documentation.
- Address vendor and cross-border transfer risks with contractual safeguards.
Learning from these enforcement cases strengthens corporate privacy strategies and reduces exposure to regulatory sanctions.
Building a Culture of Privacy Compliance
Compliance is not static—it requires continuous monitoring, updates, and staff training. Embedding privacy governance into corporate culture ensures CNIL privacy compliance becomes second nature. Organizations should:
- Document processes, maintain audit trails, and schedule periodic reviews.
- Establish privacy committees to oversee implementation.
- Integrate compliance objectives into corporate performance metrics.
- Run awareness campaigns that reinforce data protection responsibilities.
By treating CNIL privacy compliance as a cultural commitment rather than a checkbox exercise, companies can adapt quickly to evolving regulations.
Technology and Tools for Compliance
Leveraging the right tools can streamline privacy compliance. Data mapping software, consent management platforms, and automated reporting dashboards help organizations implement CNIL compliance requirements more efficiently. Automation reduces manual errors while providing regulators with clear evidence of compliance efforts. For multinational companies, these tools also simplify aligning French data protection regulations with other jurisdictions.
Conclusion
Privacy obligations in France demand rigor, but they also offer organizations a roadmap for stronger governance. CNIL privacy compliance integrates GDPR compliance steps with national enforcement lessons, creating a model for sustainable data protection. Companies that adopt CNIL compliance requirements not only reduce risk but also build trust and resilience. If your business is looking to strengthen privacy programs or align with French data protection regulations, 4Thought Marketing can help you navigate CNIL guidelines and implement best practices with confidence.