Key Takeaways
- The California browser opt-out law simplifies privacy control at scale.
- Consumers can send one browser signal to stop data sharing.
- The law limits sensitive data use across websites.
- Businesses must honor browser-based preference signal.
- Transparency and trust define the next privacy standard.
The new California browser opt-out law embeds “Do Not Sell” and “Do Not Share” privacy controls directly into the web browser itself. This approach marks a significant milestone in user-centric privacy design, while reshaping how organizations collect, share, and utilize personal information. The California browser opt-out law sets a new benchmark in enforcing user-driven privacy standards.
California has consistently led the conversation on digital privacy through the CCPA and CPRA. The California browser opt-out law extends that leadership by making privacy controls an intrinsic part of the browsing experience. The California Opt Me Out Act (Assembly Bill 566) takes that vision further, connecting existing rights to an actionable, one-click mechanism. When the law takes effect on January 1, 2027, users will be able to activate a universal signal that automatically tells websites not to sell or share their personal data. The outcome is more than convenience—it represents a recalibration of the relationship between users, browsers, and the digital economy.
What Does the Browser Opt-Out Law Actually Do?
The core of the California browser opt-out law is a built-in browser feature called the opt-out preference signal (OOPS). When users turn this setting on, it sends a standard browser-level signal to any website they visit. That signal automatically tells the business to stop selling or sharing the user’s personal information.
- The signal covers both “Do Not Sell” and “Do Not Share” requests.
- “Sell” applies when a company transfers personal data for value.
- “Share” focuses on cross-context behavioral advertising, where user data is tracked across multiple sites.
- Browser developers must give users a simple toggle to activate the signal.
- Websites receiving the signal must process and honor it automatically.
This change means that people will no longer need to search for individual ‘Do Not Sell’ option links or rely on third-party plug-ins. The browser becomes the central controller for expressing privacy preferences.
Why Was This Law Created?
For years, consumers faced “privacy fatigue.” Every website demanded another click to set data preferences. California regulators saw that as an obstacle to meaningful privacy rights.
The new opt-out framework solves that complexity. Instead of leaving responsibility to each site, it moves it to the browser level, where the user already operates. By integrating privacy rights directly into browser functionality, the California browser opt-out law removes friction and standardizes user control. The shift reflects key lessons from the past five years of privacy enforcement:
- Accessibility: Rights are only effective if they are easy to exercise.
- Clarity: One standard mechanism reduces confusion across brands.
- Scalability: A single preference signal simplifies compliance for users and businesses alike.
By standardizing opt-out behavior, the law integrates privacy into everyday browsing habits—turning abstract rights into a functional control anyone can use.
What Counts as Personal and Sensitive Information?
The California Consumer Privacy Act defines personal information broadly. Under AB 566, the opt-out signal applies specifically to personal data that could identify or profile a user, including:
- Unique identifiers, IP addresses, or contact details
- Browsing or search history
- Geolocation and device information
In addition, the law recognizes sensitive personal information—a separate category that receives enhanced protection. This includes government IDs, biometric data, health details, and precise location tracking. Through the new browser signal, users can limit how businesses use such data beyond what is necessary for legitimate service delivery.
This combination—opt-out of sale/share plus sensitive data limitations—creates the most comprehensive user control yet built into browsers.
What Challenges Will Businesses Face?
While the California browser opt-out law simplifies control for consumers, implementation is complex for organizations. Every covered business must ensure their systems detect, record, and act upon these browser-based signals accurately.
Challenges include:
- Data Integration: Connecting consent management tools, analytics, and ad platforms to honor signals automatically.
- System Synchronization: Making sure the opt-out status remains consistent across marketing stacks and vendors.
- Proof of Compliance: Being able to document that every received signal was respected.
- Strategy Recalibration: Adapting marketing methods toward contextual or consent-based engagement.
For advertisers, this may reduce the effectiveness of retargeting campaigns. However, it also provides an opportunity to deepen trust through transparent, privacy-forward design.
How Will Browsers and Mobile Platforms Respond?
Because most major browsers—like Chrome, Safari, Edge, and Firefox—are developed by companies that operate or conduct business in California, the law carries global reach. Even if the signal is designed for California users, browser makers are unlikely to limit such functionality geographically.
- Browser settings could make privacy a default feature for all users.
- Mobile browsers and operating systems may soon follow similar requirements.
- Coordinated standards across states could lead to a nationwide or even global default.
This could create de facto national alignment on privacy signals, even before Congress acts on federal legislation.
What Does the California Browser Opt-Out Law Mean for Consumers?
The California browser opt-out law transforms an abstract privacy right into an everyday user experience. When that signal is on:
- Websites must stop selling or sharing the user’s data with third parties.
- Sensitive information must be used only for essential functions.
- First-party analytics and contextual advertising can continue.
The outcome is not a total halt to data collection, but a balanced and transparent model where consent and protection follow the user, not the brand.
How Far Could This Law’s Impact Reach?
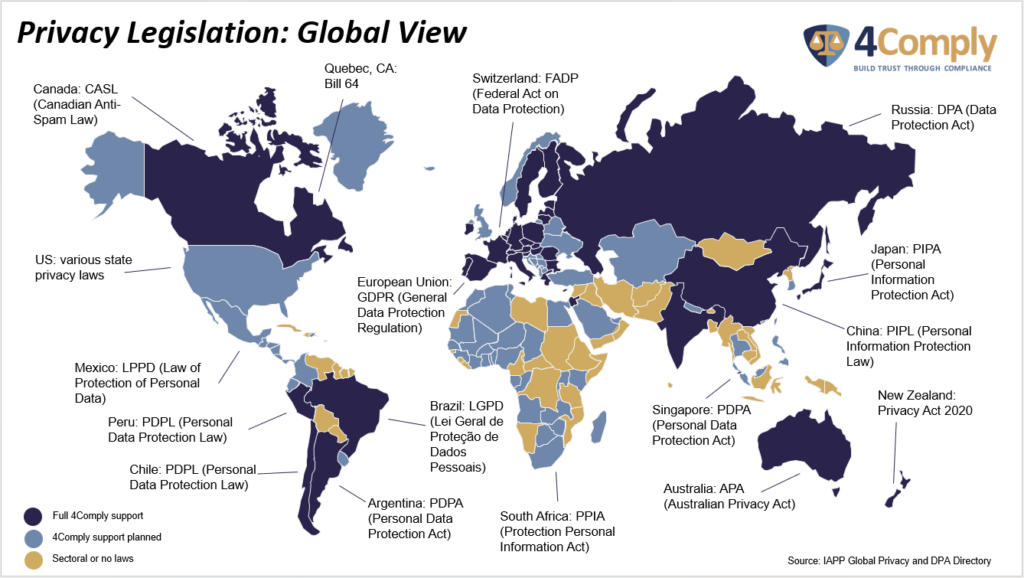
Even before 2027, the new framework may inspire similar policies nationally and internationally. Several U.S. states already require businesses to honor universal opt-out mechanisms. When browsers implement California’s mandatory signal, the feature could easily extend to those jurisdictions and beyond.
This wave of privacy standardization has strategic implications:
- Global Adoption: A default privacy control in leading browsers affects all users, wherever they are.
- Compliance Efficiency: Uniform handling of signals reduces operational costs.
- Innovation Incentive: Startups and developers can design privacy-by-default solutions that add value through trust.
AB 566 effectively turns the browser into a privacy command center, shifting the global conversation from “compliance” to “empowerment.”
Conclusion
California’s browser-based opt-out law turns an abstract right into an everyday experience. By allowing people to communicate their privacy preferences once—universally—it brings clarity to a complex digital environment. For privacy-conscious organizations, this is a call to move early, aligning systems, vendors, and messaging around transparency and respect. At 4Thought Marketing and 4Comply, our teams help businesses connect compliance with consumer confidence. Build your strategy now so trust becomes your competitive advantage when the new standard arrives in 2027.